Difference between revisions of "Smartphone"
(→Problems) |
m (→Problems) |
||
| Line 15: | Line 15: | ||
** In some cases, the SIM card in the phone may be swapped by telco for the attacker. | ** In some cases, the SIM card in the phone may be swapped by telco for the attacker. | ||
* While the solutions offered by the phone give greater security, the [[Identifier]]s protected by the phone are more tightly bound to the individual and make tracking more certain. | * While the solutions offered by the phone give greater security, the [[Identifier]]s protected by the phone are more tightly bound to the individual and make tracking more certain. | ||
| − | ** The [[Identifier]]s may be cryptographically bound to the device [[Trusted Execution Environment]] (TEE aka Secure Enclave), | + | ** The [[Identifier]]s may be cryptographically bound to the device [[Trusted Execution Environment]] (TEE aka [[Secure Enclave]]), |
** The [[Identifier]]s may be cryptographically bound to the SIM card installed in the device. | ** The [[Identifier]]s may be cryptographically bound to the SIM card installed in the device. | ||
Revision as of 17:25, 20 September 2022
Full Title or Meme
A Smartphone is a mobile device that can download Native Apps or Progressive Web Apps for contacting Web Sites as well as traditional mobile services like calling and messaging.
Context
- The computing power of a Smartphone today is beyond that of any computer of 25 years ago. The connectivity of a Smart Phone is beyond that of any computer of 25 years ago. Now anyone of modest means can carry one with them nearly anywhere they want to go. Clearly society will feel the impact of this leap of technology. And its impact for personal Identity can only be guessed at. See the appendix below for early prognostication about possibilities which are now reified in the Smartphone.
- Pew research report Enhanced Patient Matching Is Critical to Achieving Full Promise of Digital Health Records. While the report's first solution was a universal health Identifier, they realize the blockers to that in the US and the second solution was patient oriented solutions like the Smart Phone.
Problems
- Smart Phones are valuable, both in their own right, and as access to user information. Theft is common.
- SMS on the smartphone seemed attactive a second factor, but that was never supported by the telcos. This article "Can You Rely on OTPs? A Study of SMS PVA Services and Their Possible Criminal Uses" describes some of the attacks against SMS.
- Telephone numbers can be reassigned by attacks against the telco self-service web sites or even the manned service locations.
- In some cases, the SIM card in the phone may be swapped by telco for the attacker.
- While the solutions offered by the phone give greater security, the Identifiers protected by the phone are more tightly bound to the individual and make tracking more certain.
- The Identifiers may be cryptographically bound to the device Trusted Execution Environment (TEE aka Secure Enclave),
- The Identifiers may be cryptographically bound to the SIM card installed in the device.
Solutions
The Smartphone will be provisioned with a variety of Native Apps when acquired by the user. A number of these apps, like email, will require the user to sign-in using some Identifier or Attribute Provider that also provides Authentication to unrelated third parties. For example, Google Android or Apple iCloud services can be sued to sign-in to sites that recognize the OpenID Connect protocol that they use.
The Smart phone is now the Identity in Everyone's Pocket[1]. The linked article shows how the Smartphone helps to keep users secure for both Identity and Privacy. It is written from the point of view of an app developer and focuses on how that developer can use the occasionally inconsistent platform capabilities from Apple and Google.
Smart Phone role in Authentication
The Smart Phone can serve a variety of roles in the process of Authentication of the user and Authorization of user access to User Information held on Web Sites. The major services are these:
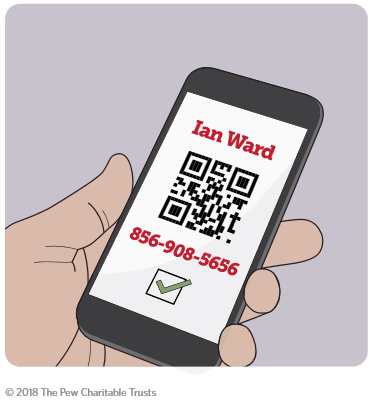
- The phone can store authentication information that is displayed to a reader in a physical device owned by the Relying Party. The information may include the user name only or user name and password or other authentication information.
- The phone supports blue tooth and payment NFC protocols that can be sued in a reader in a physical device owned by the Relying Party, or on the user's desktop computer.
- An Authentication Native App can be loaded onto the phone from existing Authentication providers, like Microsoft or Google.
- The secure storage of credentials, as described in the following section, can greatly improve the security of the Authentication process.
- Biometric sign-in capabilities of the Smartphone can be reported to the website for proof-of-presence, a very valuable additional authentication factor.
Smart Phone Hardware Security
- Hardware Protection has been a security gold standard since the advent of FIPS 140, but it must be remembered that their is no longer any such thing as a purely hardware component in computer design. All sophisticated hardware chips now contain significant software components and many contain configurable memory, or firmware, that contains software that is "just" a part of the hardware. This is commonly referred to as a Trusted Execution Environment.
- The Trusted Platform Module TPM was a hardware chip in version one, but by 2020 all Intel and Android processors included secure hardware that could run the version two TPM as software in the secure environment. The TPM can make a statement about the software operating system that a Remote Attestation Service can verify.
- Security Enhancements (SE) for Android was a NSA-led project that created and released an open-source reference implementation of how to enable and apply SELinux to Android, made the case for adopting SELinux into mainline Android, and worked with the Android Open-Source Project (AOSP) to integrate the changes into mainline Android. As a result, SELinux has been a core part of Android since 2019. See https://source.android.com/security/selinux/ for further information on SELinux in Android.
- Android security program.
Smart Phone storage of user information
The Smart Phone can both collection user information from a variety of sources and then turn around and send that data to web sites that need the information. This process of sourcing and sinking data can be entirely on the Smart Phone itself, or in conjunction with a Web Site that acts as a back-end for a Web App on the phone.
Proof of Presence
- There are a variety of sensors on many smartphones that can be used as authentication factors or more.
- The Biometric input of (for example) face scans or fingerprints and provide a link to the physical human presence.
Trust of the Data
- Any smartphone app (native or web) can send any data it wants to any web page it can access.
- How then can a Relying Party accept a statement from a phone app?
- The statement itself can be signed by a trusted issuer.
- The phone app can prove its reliability by some assessment process.
Trust of the Web Site
- If the user doesn't really know the identity of the web site that they are communicating with, no rational decisions are possible.
Transport Layer
There are several types of support for identity and privacy that can be acquired from the transport layer. But a warning is in order. The context between the application layer and the transport layer offers an additional attack point that is hard to discover.
- The first layer of web site identity is the URL, which is far less reliable since the internationalization of the URLs allow for strange mixtures of alphabets that the user might not discern.
- Some early attacks on the DNS made the URL less reliable, but most of these are being addressed by secure DNS.
- Token Binding is an attempt to use the HTTPS binding with an application-level token.
- mTLS or mutual TLS allows the binding of the DNS name of the web site to all interchanges.
Appendix
History of the Idea
- The idea of a "World Brain" was published as a book by H. G. Wells in 1920.
- In 1926 Nikola Tesla was quoted saying that
When wireless is perfectly applied the whole earth will be converted into a huge brain, which in fact it is, all things being particles of a real and rhythmic whole. We shall be able to communicate with one another instantly, irrespective of distance. Not only this, but through television and telephony we shall see and hear one another as perfectly as though we were face to face, despite intervening distances of thousands of miles; and the instruments through which we shall be able to do his will be amazingly simple compared with our present telephone. A man will be able to carry one in his vest pocket.
- After acting as chief of the U.S. Office of Scientific Research and Development during WW II, Vannevar Bush in his 1945 article "As We May Think" wrote about the "Memex" which was a table-sized version of a device that would perform feats that are now possible with a Smartphone.
Smart Phone Screen Sizes
- Media Genesis has a good list. also Device Atlas
- iPhone 5 640 x 1136 pixels 320 x 568 view port
- iPhone 7+ 1080 x 1920 pixels 414 x 736 view port
- Google N5X 1080 x 1920 Pixels 412 x 732 VP
- Google 3XL 1440 x 2960 Pixels 412 x 846 VP
- Samsung S7 1440 x 2960. pixels 360 x 640 VP
Premium phone can go somewhat higher and even have two screens folded together in 2021.
The viewport is the user's visible area of a web page. It varies with the device and will be smaller on a mobile phone than on a computer screen. HTML5 introduced a method to let web designers take control over the viewport, through the <meta> tag. Note that device width changes from portrait to landscape orientation of the device. You should include the following <meta> viewport element (exactly as shown) in all your web pages:
<meta name="viewport" content="width=device-width, initial-scale=1.0">
References
- ↑ Phil Vachon, The Identity in Everyone's Pocket CACM 64 no 1 (2021-01)