Passkey
Full Title or Meme
As the name Passkey suggests, it requires dual verification of an account before someone can sign-in to that account.
Context
With Passkeys there’s a subtle difference to FIDO 2.0 as it surrounds a multi-device Fast Identity Authentication with another protocol. Passkey uses a notification, which is generally sent to an individual’s smartphone during a log-in process and lets them authenticate their credentials. Often, this is done using a PIN or biometric process and thereby removes the need for conventional letter and number combination passwords.[1]
FIDO2 specifies the Web Authentication JavaScript API standard — commonly referred to as WebAuthn — and FIDO’s corresponding Client-to-Authenticator Protocol (CTAP). See the wiki page for the latest WebAuthn 3.
Using the Javascript API, developers can leverage either hardware keys (known as roaming authenticators) or secure hardware on the device (known as platform authenticators), the latter of which are often gated by biometric sensors, to authenticate users in a passwordless manner.
- State of Passkeys according to the guys that created the thing. 2024-04
- Passkeys primer from Okta 2024-08
Features
- Originally Passkeys were device bound and could not be moved between devices.
- Passkeys since 2024 can be synced between devices that have enabled syncing. This feature can be blocked by using device-bound Passkeys. Multi-device credentials had been the name on introduction to distinguish it from the original device-bound Passkey.
- The user must unlock the passkey on the device before it is used. Typically a Biometric Factor or pin is used as a second Authentication Factor.
Multi Device Passkeys
- 2025-05 Single device vs multi device credentials Yubikey
- 2024-09, passkeys can be synced within the ecosystems of Google, Apple, and Microsoft, but cross-platform synchronization (between Google, Apple, and Microsoft) is not yet fully supported. Each company has its own system for managing and syncing passkeys:
- Google: Passkeys are synced across devices using Google Password Manager.
- Apple: Passkeys are synced across Apple devices using iCloud Keychain.
- Microsoft: Passkeys are managed and synced through Windows Hello.
- While the FIDO Alliance is working towards a unified standard for password-less authentication, full interoperability between these ecosystems is still in progress. For now, you’ll need to manage passkeys separately within each ecosystem.
Problems
- I Stopped Using Passwords. It’s Great—and a Total Mess Wired 2024-02
- The credentials created by a web connected user on a browser are completely useless when the underlying protocol insistes on some complex format like SD-JWT.
- Misconceptions about passkeys or not?
- FIDO requires secure origin binding and TLS. But that is not accessible to all password managers, so a man-in-the-middle-attack only requires spoofing the origin to be part of the origin used for the key. (in other words, the FIDO binding does not seem to apply to what happens in the xxx-manager unless the xxx-manager is fully integrated into a browser that is FIDO compliant)
Support Infrastructure
Most deployments of passkeys assume that issues with the infrastructure and user education will be solved by others. It doesn't work that way.
They’re failing because the real bottlenecks sit somewhere else entirely.
Over the past months, we’ve been collecting insights from major banks across Europe, APAC and North America and the patterns are surprisingly consistent.
If you're evaluating passkeys, these 5 realities will decide whether your rollout succeeds or stalls:
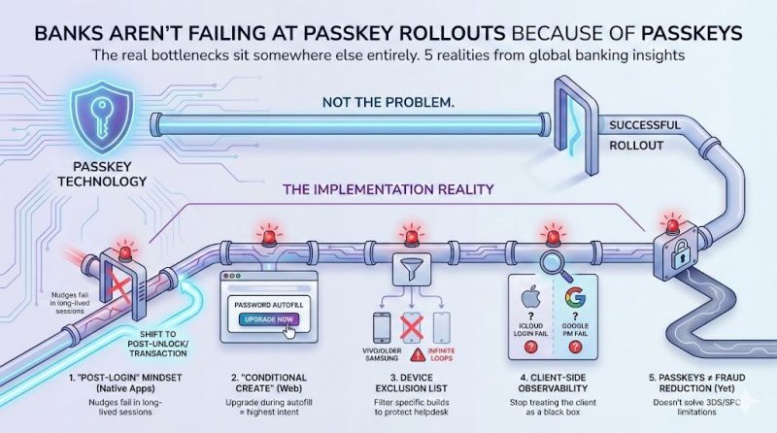
Post-Login" mindset in native apps:
Standard "post-login" nudges are failing in banking apps because users rarely perform a full login - they stay in long-lived sessions. The highest performing solution is to move the nudge to the Post-Unlock event (immediately after Face ID / biometric check) or Post-Transaction screens. This simple shift is moving activation rates from negligible to high rates for existing users in a short period of time.
Conditional Create is essential on the web:
If you’re not upgrading users during password autofill, you’re missing your highest-intent moment.
It’s low-friction, high-quality and complex, unless you anticipate browser issues and shared-device risks.
run a device exclusion list
Generic rollouts cause infinite login loops specific Android builds. We’ve found that blindly allowing all devices leads to infinite login loops (on some devices). You must be able to filter out specific new models (currently seeing high failure rates on specific Vivo builds and older Samsung Pass agents) to protect your helpdesk.
Client-side observability is non-negotiable
Most banking identity teams treat the client-side as a black box. If you can’t see why and when e.g. an iCloud login user failed vs. a Google Password Manager user, you can’t debug your implementation.
Passkeys ≠ fraud reduction (yet)
A major pain point we see banks discover too late: passkeys do not currently solve 3DS challenges due to technical 3DS limitations and the same time you cannot rely on Secure Payment Confirmation (SPC) as it is not production-ready and will not be supported by Safari/Apple at the moment.
Acceptance
- Passkeys support by both Apple and Google. See the website for details.
- By the end of 2023 it looks like more people are using passkeys than expected.[2]
1Password experienced a particular spike in October 2023, correlating with big companies like Amazon and WhatsApp rolling out their support for passkeys during this month, with over 70,000 created between October 16-22 alone.
- Public preview: Expanding passkey support in Microsoft Entra ID 2024-05-02
Solutions
- 2025-09-01 Consumer Password and Passkey Trends: World Passkey Day 2025
- 25-01 Paypal promotes passkeys for payments.
- 24-09 Allow passkey reuse across your sites with Related Origin Requests but what, exactly, is a related origin? See wiki page Browser Origin Policy.
- 24-08-08 New CISA Guide Calls for Phishing-Resistant Forms of Authentication and Passkeys by Default.
- 24-08-05 passkeys.dev now has a hashtag#WebAuthn feature detection page for developers! This page will check for common features and capabilities used with hashtag#passkeys in the browser where it was loaded! Check it out WebAuthn Features and Capability Detection] (short URL is passkeys.dev/fd)
- 24-08-04 Chrome on Android now integrates the Credential Manager allowing third-party password managers provide passkeys on Android 14 and later. With this update, your Chrome on Android 14 and later can create and save a passkey to a third-party password manager, or authenticate using a passkey saved there. Also, learn how a relying party can detect which password manager a passkey is created at.[3]
Portability
Vendor Relationship Management (via Doc Searls) is coming true but it is fully hidden behind terms like:
- Password Management,
- Credential Management,
- Portable Passkeys.
But the point is that a human being can move their access and metadata about the sites that they visit as a part of their daily life. I hope it works out! I hope they make the result extensible. See this video clip from Rew Isalm and Nick Steele.
References
- ↑ FIDO Passkeys - Accelerating the Availability of Simpler, Stronger Passwordless Sign-Ins https://fidoalliance.org/passkeys/
- ↑ Lewis Maddison, Looks like more people are using passkeys than expected 1Password sees passkeys exceed 700k (2023-12-21) https://www.techradar.com/pro/security/looks-like-more-people-are-using-passkeys-than-expected
- ↑ Eiji Kitaura, Passkeys UX updates on Chrome on Android https://developer.chrome.com/blog/passkeys-on-credential-manager
Other Material
- For a more generic solutions check out this wiki page: Vendor Relationship Manager,