Difference between revisions of "Policy-Based Access Control"
From MgmtWiki
(→XACML) |
(→XACML) |
||
| Line 8: | Line 8: | ||
==Existing Languages== | ==Existing Languages== | ||
===XACML=== | ===XACML=== | ||
| − | * [http://docs.oasis-open.org/xacml/3.0 | + | * [http://docs.oasis-open.org/xacml/3.0/xacml-3.0-core-spec-os-en.doc XACML 3.0 core spec.] |
| + | * This spec is written in XML with no regard of size of the message. It can easily be converted to json and this a a spec that describe the process. | ||
| + | * While it is oriented to an overly complex structure using monolithic designs, it has well-thought out elements that should remain useful. | ||
| + | |||
===Drools=== | ===Drools=== | ||
(which is open) | (which is open) | ||
Revision as of 16:00, 13 December 2021
Contents
Full Title or Meme
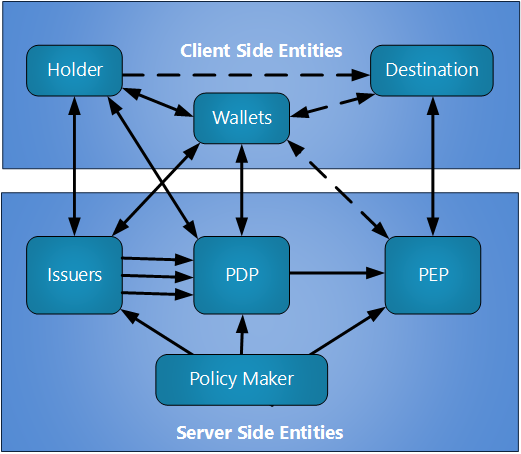
Policy-Based Access Control or PBAC is any system where Access is mediated by Access Tokens that are evaluated by a digital policy language and policy control engine.
Context
- The most common Attribute-Based Access Control language XACML expanded their scope in version 3.0 to include the description Policy-Based Access Control although policy statement was defined in earlier versions.
Existing Languages
XACML
- XACML 3.0 core spec.
- This spec is written in XML with no regard of size of the message. It can easily be converted to json and this a a spec that describe the process.
- While it is oriented to an overly complex structure using monolithic designs, it has well-thought out elements that should remain useful.
Drools
(which is open)