Policy-Based Access Control
Contents
Full Title or Meme
Policy-Based Access Control or PBAC is any system where Access is mediated by Access Tokens that are evaluated by a digital policy language and policy control engine.
Context
- The most common Attribute-Based Access Control language XACML expanded their scope in version 3.0 to include the description Policy-Based Access Control although policy statement was defined in earlier versions.
Existing Languages
These are all written by geeks, and for geeks. What is needed is some policy that works in a real-world user journey. In other words, the user needs to be able to understand what is expected and when.
Cardea
They have been working with the government of Aruba and come up with most through look at the problem in 2022. The have picked the unfortunate name of Machine Readable Governance, but it really is a description of the government's policy. Unfortunately, it might change daily and does not meet the requirement of testing by the user and remaining valid for even the duration of a flight from the US to the island.
- Machine Readable Governance. A JWT with a mishmash of different levels of abstraction from human readable questions to access policy.
- Cardea on GitHub.
XACML
- XACML 3.0 core spec.
- This spec is written in XML with no regard of size of the message. XML can easily be converted to json and this is the spec that describes that process.
- While it is oriented to an overly complex structure using monolithic designs, it has well-thought-out elements that should remain useful in the domain where it was applied. It is less useful in new areas like application of areas like COVID Vaccination.
- A lot of the language used below is taken from the XACML spec. For example:
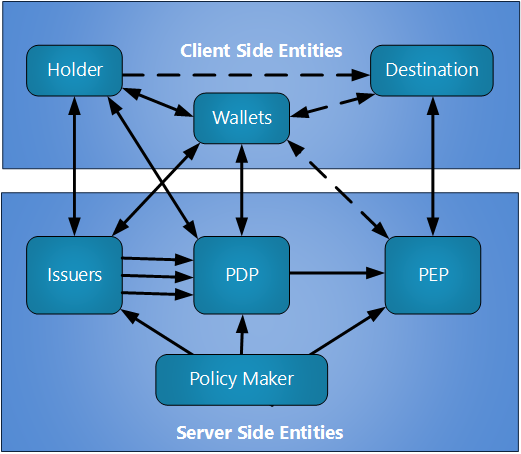
- PDP = policy definition point
- PEP = policy execution point
LegalRuleML
Is also an OASIS spec that attempts to turn law into machine readable format. This wiki page is focused more on the application of the policy to access control.
- Converting law, writen in English (in the US) to a policy to be applied for access control is insanely difficult.[1] Typically the programmer will be given a design document that is coded and ship before the lawyers are asked to adjudicate some discrepancy. Trying to engage the lawyers at the start of the process might sound better, unless you were a program manager with a schedule to keep. And a policy is a basically a programmer's view of the policy in the spec. The likelihood of error is close to one. Adam Wyner commented:
It is very welcome to see a discussion in the ACM about artificial intelligence/computer science applied to law. Applications to tax go all the way back to 1977 with the Taxman system and subsequent work: https://www.jstor.org/stable/1340132 Further work on AI and Law can be found on the International Association for Artificial Intelligence and Law: http://www.iaail.org/ and the Journal of Artificial Intelligence and Law: https://www.springer.com/journal/10506
Drools
- Supposedly this is open, which apparently applies to the java code implementation which is at the follow site.
- Drools documentation.
- "Drools is Rule Engine or a Production Rule System that uses the rule-based approach to implement and Expert System. Expert Systems are knowledge-based systems that use knowledge representation to process acquired knowledge into a knowledge base that can be used for reasoning."
- The rules supported by Drools look a lot like a domain specific programming language, not a business rules language.
HL7 CQL
- Clinical Quality Language (CQL) is a high-level, domain-specific language focused on clinical quality and targeted at measure and decision support artifact authors.
- In addition, this specification describes a machine-readable canonical representation called Expression Logical Model (ELM) targeted at implementations and designed to enable sharing of clinical knowledge.
Solution
This wiki page is interested in the machine-readable policy language and how it can be applied to access control.
Policy Distribution
Policy can be made at the government level or by a resource owner. When a user is attempting to access some digital resource or some real-world venue, it is typically important for the user to know if they have the credentials to achieve their objective in advance. For example, in the Biometric Pre-Check use case the traveler (denoted as the holder in the image below) is expected to be able to determine if they can pass through the check-in line before they even leave home for the airport. The solid lines in the figure below are data transfers. The dotted lines are physical presentations, not all of which are required in every case.
User Experience
It is expected as the Mobile Driver's License become commonly available that identity and health credentials will generally be available in the holder's Smartphone.
References
- ↑ Esther Shein, Converting Laws to Programs CACM 65 No 1, pp 15-16 (2022-01) Communications of the ACM Vol. 65 No. 1, Pages 15-16 https://m.acmwebvm01.acm.org/magazines/2022/1/257436-converting-laws-to-programs/fulltext
Other Material
- For policy applied at the web page origin see the wiki page on Content Security Policy.